
Document Verification: Identify with Confidence.
Powering Trust for Every Customer Journey.
Government-issued documents are the primary trust signal in digital onboarding and also a prime target for fraud. IDnow Document Verification instantly checks the authenticity, integrity and ownership of passports, ID cards, residence permits and other official documents across channels and use cases. Fast, compliant and fraud-resistant, it converts documents into reliable identity decisions.
We design document verification to fit the risk and requirements of your business, so you get friction-free paths for low-risk flows and stronger assurance where it matters most, not a one-size-fits-all solution, but the right fit for your business and your customers.
Deploy Trust, Your Way.
Automated Verification
Fast, guided capture for web and mobile that returns results in seconds. Leveraging technologies such as advanced image analysis and OCR, our fully automated checks work behind the scenes to extract and assess document data, flag anomalies, and route only the high-risk cases for further review – keeping friction low for genuine users while scaling to handle volume.

Video Verification
For highly regulated industries, high-risk transactions or complex edge cases, we have over 775+ trained identification specialists, located in 12 centers across 8 countries, who carry out live document inspections via video. They guide users to present documents to the camera, verify visual security cues and compare the document to the live person, innovatively combining human judgement and expertise with AI controls for the highest assurance possible. Depending on regulation requirements or business preferences, you can choose specialists in or outside the EU.

Point-of-Sale Verification
At branches, kiosks or retail counters, bring the same digital-grade checks to in-person interactions. Capture on-device, run layered checks and provide decision-ready results and clear escalation paths, so you can verify identity reliably at the point of interaction.

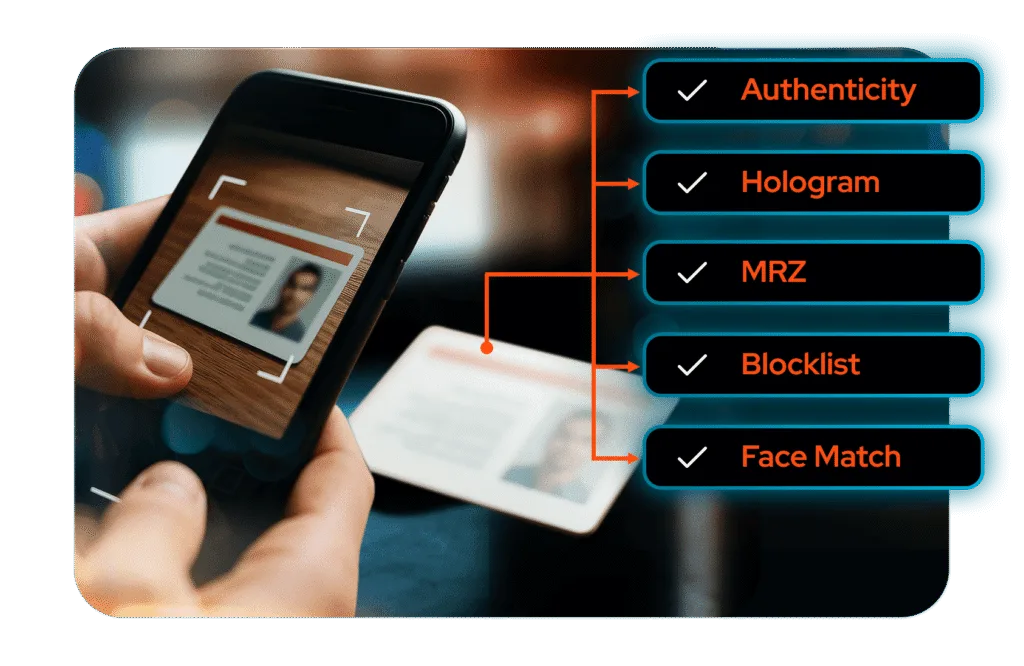
What We Analyse:
We run hundreds of checks – visual, algorithmic, structural, biometric and behavioural – to ensure documents are valid, authentic and not a fraudulent creation.
Reality Check: Fraud in Action
A customer submits what looks like a genuine ID, but our system detects an expiry date format inconsistent with that country’s official template. We flag and block the onboarding instantly.
Reality Check: Fraud in Action
A passport’s hologram alignment is just a fraction off and the microtext is missing – enough for us to identify it as a forgery and stop the attempt.
Reality Check: Fraud in Action
A user submits an ID document where the machine-readable line and the NFC read-out do not match – the document is flaged as fraudulent and rejected.
Reality Check: Fraud in Action
A user presents a ID document and attempts to submit a static image of the ID holder at the biometric check. This fails the liveness detection test and is flagged as identity theft.
Reality Check: Fraud in Action
An ID number has been used in three prior onboarding attempts under different names. Our system spots the reuse instantly and stops the fraudulent attempt instantly.

Why Businesses Choose IDnow Document Verification:
Global document coverage for thousands of document types and formats
775+ trained verification specialists in Europe and worldwide
Built-in fraud detection using visual, structural and behavioral signals
Fully automated, expert-assisted or point-of-service verification flows
Compliant with eIDAS, AML, KYC, GDPR and other global regulations
Easy integration via SDK, API or the IDnow Trust Platform
Most Common Identity Documents:
Passport.
Identity Card.
Residence Permit.
Driving License.
Health Insurance Card.
Other supporting documents.
From First Glance to Final Approval.
We turn documents into meaningful identity signals, not by relying on a single check, but by combining innovative AI technologies, our market-leading fraud intelligence expertise and highly-trained specialist oversight where required. The result: higher conversions, seamless, secure user experience and auditable outcomes you can trust.

Built to Work in Your World.
Integrate Document Verification into your existing workflows with minimal effort. Whether you need an SDK, an API or orchestration through the IDnow Identity Trust Platform, we provide scalable, privacy-first identity checks that meet the needs of modern digital businesses.
Confidence in every check.
Turn documents into trust decisions.
Whether it’s passports, ID cards or residence permits, IDnow turns documents into verified trust signals in seconds. With global coverage, advanced fraud detection and compliance baked in, we keep your onboarding fast, secure and compliant.
